The Shadow Automation Layer
Your team is already running automations you don't know about. That's not the problem.

They didn’t ask permission because asking would have taken longer than building it.
That’s the whole story. Not a security failure. Not recklessness. A resource allocation problem that nobody solved, so people solved it themselves.
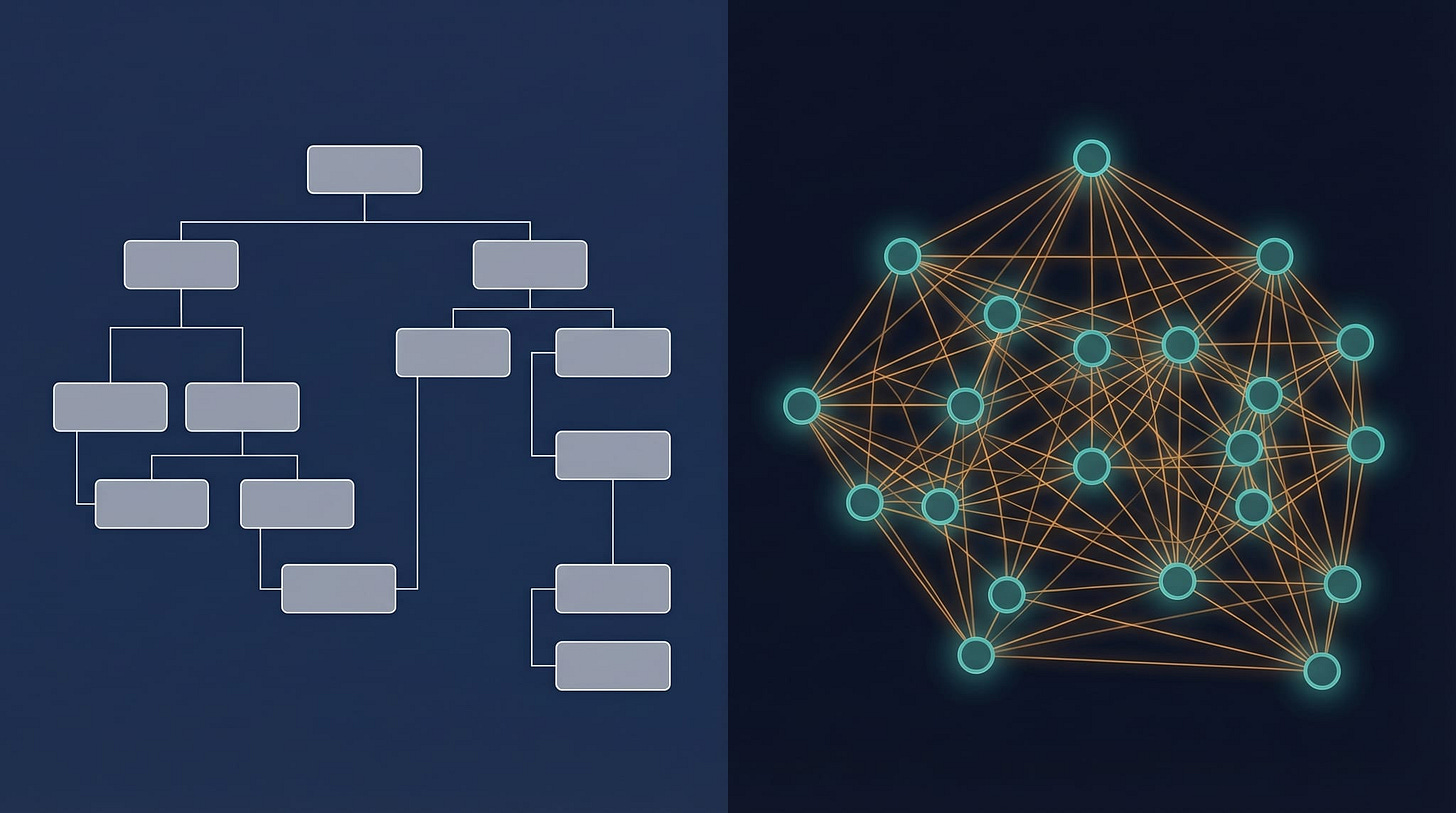
The shadow automation layer is what happens when official tooling is too slow, too expensive, or too bureaucratic. Someone writes a script. Someone sets up a personal API key. Someone builds a prompt chain in a free-tier tool that sends emails, updates spreadsheets, or summarizes meetings without appearing in any system of record. It runs quietly. It handles real work. It doesn’t appear on any inventory.
This is common. Surveys of enterprise SaaS environments consistently find that a majority of tools in use are unknown to IT departments. That number was collected before AI dropped the barrier to building automation from “knows how to code” to “knows how to describe a problem.”
WHY IT EXISTS
Shadow automation is not defiance. It’s a symptom.
The official path was too slow. Or the approved tool didn’t do the thing. Or the thing was so obviously right that waiting for approval felt like a tax on results.
The people building shadow automation are almost always the high performers. They found a gap between what the system supports and what the work requires. They filled it. That’s not recklessness. That’s the same instinct that builds good products: notice friction, remove it.
Friction Is a Vulnerability made this case directly. Friction doesn’t stop the action; it reroutes it through a workaround. The workaround is usually unobserved. Unobserved work doesn’t get evaluated, improved, or governed.
The shadow automation layer is friction’s direct output.
THE ACTUAL RISKS
Not what you’d expect.
The risk isn’t that AI tools hallucinate in production. Hallucination is loud. It fails visibly. The real risks are quieter.
Blast radius. Nobody knows what the automation touches. When it breaks, nobody has a map of downstream effects. A script that seemed to update one spreadsheet turns out to be the upstream source for three other processes that nobody documented.
Auditability. Shadow automation leaves no receipt. Receipts Everywhere established what makes a record trustworthy: it’s hard to modify without detection, and you can produce it on demand without asking permission. Shadow automations produce neither. They log nothing. When something goes wrong, the investigation starts from zero.
Single-human dependency. The person who built it is the only one who understands it. When they leave, the automation becomes a black box everyone is afraid to touch. It doesn’t fail immediately. It fails incrementally, in ways that are invisible until they compound.
These risks don’t require AI. They exist with spreadsheet macros, shell scripts, and personal Zaps. AI accelerates the pattern because the tools are more powerful and the entry barrier is lower.
THE GUARDRAILS THAT ACTUALLY WORK
Banning the tools doesn’t work. The friction increases and the shadow layer moves further underground.
Three questions determine whether a shadow automation is governable:
What is it allowed to touch? Scope creep in automation is silent. An automation that starts by summarizing emails ends up archiving them. Define the surface at the start, not after the incident. This is the blast radius question. Write it down before you build, not during the postmortem.
How much can it change in a single run? Recovery-First Automation built the case for rate limits as a feature: if you can’t undo it, you must slow it down. Shadow automations almost never have rate limits. Applying one, even a manual checkpoint or a cap on how many records a single run can affect, constrains the blast radius before it matters.
Where does it write its record? The Local Logbook ended with a checklist. Automation that doesn’t write a local record of what it did and what it changed doesn’t get to claim the reliability benefits of the local-first stack. An automation log is not a debugging artifact. It’s the receipt you’ll need when the investigation starts.
These three questions don’t require a policy document. They require five minutes at the start of the build.
That’s not bureaucracy. That’s the minimum viable container for anything that runs unsupervised.
THE PATTERN YOU’RE BUILDING TOWARD
The past several weeks have been building toward the same point from different angles.
Local-first isn’t anti-cloud; it’s a reliability decision. The logbook isn’t surveillance; it’s evidence you control. The shadow automation layer isn’t rogue; it’s speed without a container.
The container is what you’re designing when you answer those three questions.
Next week is the capstone: what it looks like when these pieces come together. The automation layer, the logbook, the local-first habits: a personal operating system you can reproduce. Not an inspiration essay. An artifact.
The governance conversation around AI tools keeps getting framed as a policy problem. Ban this. Require approval for that. Audit quarterly.
That’s the wrong frame.
The automation running inside your organization without IT’s knowledge isn’t running there because your employees are reckless. It’s running there because the official path was too slow and the work still needed doing.
The question isn’t whether to allow the tools. The tools are already there.
The question is what the automation is allowed to touch, how much it can change in a single run, and where it writes the record of what it did.
Govern outcomes and blast radius, not tools.
Resources
Morphic: Friction Is a Vulnerability: Why friction doesn’t prevent unsafe workarounds. It reroutes toward them. The shadow automation layer is friction’s direct output.
Morphic: Recovery-First Automation: Undo Is the Feature: Rate limits and undo windows as design constraints, not afterthoughts. Applies directly to shadow automation blast radius.
Morphic: Receipts Everywhere: Trust Without Central Trust: The receipt model for verifiable audit trails. Shadow automations leave none by default.
Morphic: The Local Logbook: Evidence That Doesn’t Need Permission: Automation that doesn’t write a local record doesn’t get to claim the reliability benefits. The logbook is the prerequisite.
Gartner: Citizen Development and Shadow IT: [Please Verify Link: Gartner definition and research on citizen development and shadow IT prevalence]: Gartner research on the prevalence and risks of unsanctioned tooling in enterprise environments. Verify current report URL before publishing.

